|
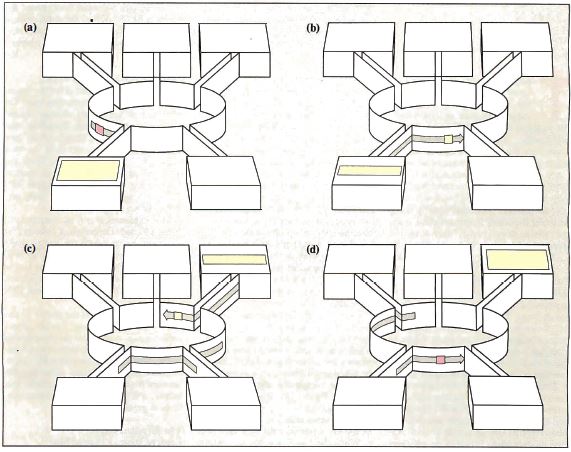
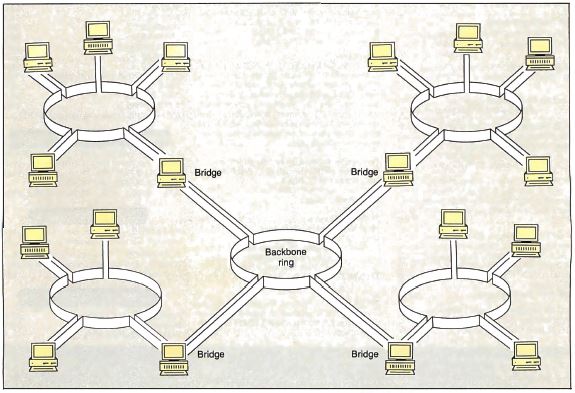
Figure 1: A
functional overview of the Token Ring. (a) The sending
station waits for a token; (b) the sending station makes
the token a frame by adding addresses and data; (c) the
receiving station copies data and sets the "copied bit";
and (d) the sending station removes the data and
generates a new token. (Figure courtesy of IBM Corp.) Each node receives information from one of its
neighbors (its nearest active upstream neighbor, or NAUN
for short) and transmits it to the node immediately
downstream. Unless a node is transmitting its own data,
it passes on whatever information it receives from its
NAUN verbatim. Thus, any node can transmit information
to any other node by sending it through some or all of
the others. The total effect resembles an endless,
circular version of the party game Telephone, in which
players occasionally add their own information to the
circle. This is the ring part of the Token Ring.
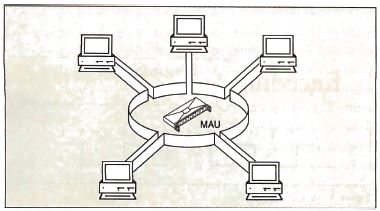
Figure 2 : At the lowest level, the physical layer, a Token Ring looks like a star (hence the term "star-wired ring topology ") in which each node is connected to a wiring concentrator, the medium access unit. Each network node uses a single two-pair cable to
connect to a device called a wiring concentrator, or, in
Token Ring parlance, a medium access unit (MAU). One
pair is for receiving data, the other for sending data.
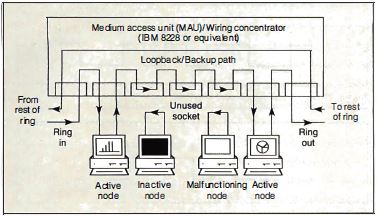
Figure 3: Signal flow in the medium access unit. Note that any or all nodes in the star-wired ring can be bypassed if necessary. When you turn a workstation off or when a node leaves
the ring because of a malfunction, current ceases to
flow in the "phantom circuit" (see figure 4) associated
with that node. A relay opens in the MAU, and the ring
reconfigures itself without the inactive machine. 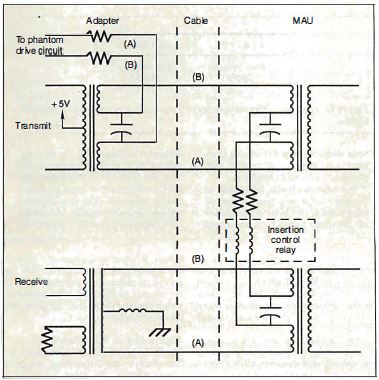
Figure 4: The
"phantom circuit " is essential to ring maintenance. If
a node is on a damaged section of the ring or if
requested by the local-area-network management program,
a node removes itself from the ring by removing its
voltage from the circuit (deactivating the phantom
circuit). The presence of too much or too little current
in the phantom circuit indicates a wiring problem.
(Figure courtesy of Texas Instruments.) If only one MAU is in the network, the MAU configures
all the stations attached to it into a ring. If there is
more than one MAU, each links its stations into a single
ring that runs through all the MAUs.
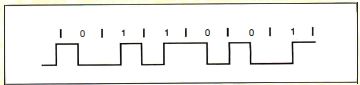
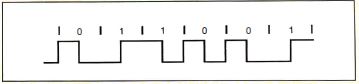
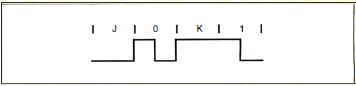
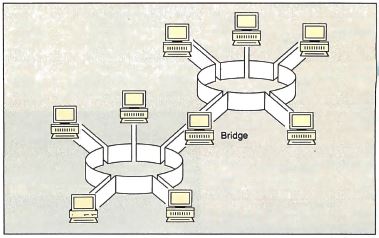
Encoding (Spreads
across 366 and 367)
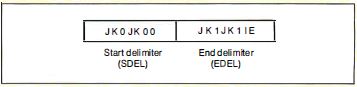 Figure D: The abort delimiter consists of a start delimiter and an end delimiter together. When a node that wants to transmit receives a token, it changes the token into a frame, appending its address, the recipient's address, and the data (see figure E). The frame also contains a redundancy code, and a status byte. 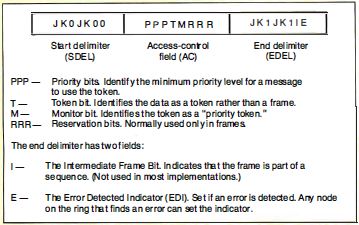 Figure E: Token format. In the event that a node needs to abort a transmission in the middle, it sends an abort delimiter sequence, which consists of the start delimiter and the end delimiter together (see figure F). 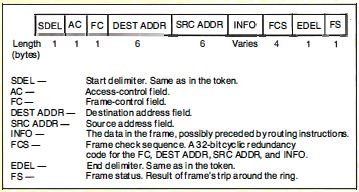 Figure F: Frame format. The MAC Sublayer Let ' s examine the signals the Token Ring's physical medium carries and the techniques used to arbitrate access to the ring: the media access (MAC) sublayer. Data is transmitted on the ring using differential Manchester encoding (see the text box "Encoding" above) , typically at 4 megabits per second (IEEE will release a 16-Mbps Token Ring standard soon). When the ring is idle, the stations on the ring continuously relay a token (sometimes called a "free token") to one another. When a node that wishes to transmit receives a token, it examines the priority bits to make sure its message has a priority at least as large as that of the token. If it does, it converts the token into a frame. Occasionally, a node will "decide" to abort a transmission in the middle. To do so, it sends an abort delimiter sequence, which consists of the start delimiter and the end delimiter together. Addressing on the Token Ring The IEEE 802.5 specification allows address sizes on the Token Ring. Besides a 6-byte address (the same length as in other IEEE standards), "short" 2-byte addresses are available for small networks. The source address and destination address fields of a frame can do more than identify a• single sender and recipient for the frame. The most significant bit of a source address is the routing information indicator, used when two or more rings are interconnected by nodes called bridges. When this bit is a 1, it indicates that the frame will specify not only the address of the destination node, but also a route to it-possibly spanning several rings. This technique is called source routing. Because the route is already worked out, the job of a bridge is simple. All it needs to do is follow the sender's routing instructions, which are tacked onto the beginning of the INFO field. Destination addresses also have bits and bit patterns with special significance. It's possible to earmark frames for a server, a group of nodes, or all nodes (a broadcast address). Functional addressing is a powerful feature built into every Token Ring adapter. By sending a frame to a functional address, a node can use network services-like a parameter server, an error monitor, or a network manager without knowing the address of the nodes that provide those services to the ring. The Active Monitor So far, most of the features I've looked at assume that the ring is up and running properly. But what if something goes wrong? When you first bring the ring up, or when any malfunction requires reconfiguration, the nodes on the ring test their equipment and send signals to one another to identify their NAUNs. The nodes select one node (normally the active node with the numerically largest address) as the active monitor. This node is designated to perform special "watchdog" functions. The process by which neighbors are identified and the active monitor is chosen is called "beaconing." Once the active monitor has been chosen, it clears the ring and issues a token to restart normal ring operation. The most basic function of the active monitor is to provide a clocking signal for the Token Ring. All other stations on the ring "listen" to this signal and synchronize with it. (The active monitor uses its own crystal to clock the data it transmits.) The active monitor's next responsibility is to ensure that a token is circulating on the ring. First, the active monitor has to make sure that the token "fits" on the ring by introducing a 24-bit shift register into the ring. (Each node is designed to incur a minimal delay, typically 1 to 2 bit times. The wiring of the ring may not have 24 bits of delay all by itself. If the signal travels on the ring at two-thirds the speed of light, the ring needs to be 2/3 X 3 X 10(8) meters/second X 24 bits / [ 4 X 10(6) bits/ second] long, or at least 1200 meters long, for the wiring to delay the signal 24 bit times.) The active monitor also watches for "lost tokens. " If it does not see a frame or a token go by within any 10-millisecond period, it clears the ring and starts a new token circulating. These actions keep the token from being irretrievably lost if a station fails to retransmit it. The active monitor checks for frames and priority tokens (tokens with a priority greater than 0) that circulate around the ring more than once. It does this by checking the setting of the monitor bit in the access control (AC) field of each token or frame it sees. If the active monitor receives a priority token or frame with the monitor bit cleared, it sets the bit as it passes on the information. If the token or frame returns when it should not, the active monitor will discover that the monitor bit is already set to 1, and it will immediately purge the ring of data and restart the token-passing process. Finally, the active monitor must "re-assure" the other stations on the ring that it is present and working. To do this, it broadcasts an active-monitor-present frame to the rest of the ring. If an AMP frame fails to circulate every so often, another station (the standby monitor) takes over the active monitor's job. A Matter of Priority On most other LANs, all nodes compete on an equal basis for use of the physical medium. For instance, there 's no way for an Ethernet station to say, "I have a very important message to send; please let me go next! " As an Ethernet gets crowded with traffic , it becomes likely that collisions, or just bad luck, will cause a delay of high-priority messages. We say that networks like the Ethernet are not "deterministic" -there 's no upper bound on the amount of time it will take a node to gain access. In some situations, like sensitive control application s, the delays can be disastrous. Some networks are deterministic but lack priority structures. ARCnet, which is a token-passing bus network, guarantees that each node can talk in turn, but the turns are always distributed evenly. There 's no provision for getting an urgent message to its destination faster. The Token Ring, however, has a unique scheme that provides for multiple priority levels and egalitarian, round-robin access on each level. The key to this scheme is the AC field present in each token or frame, which carries priority information and accepts "reservations" for the next use of the token. After a station transmits a frame, it examines the AC field when the frame returns. If the reservation bits of the AC field contain a number greater than the priority level on which the station is currently transmitting, it means that one or more nodes wish to transmit at the higher priority as soon as possible. The sender emits a token with the higher priority. Since a station can use only a token that has a priority less than or equal to the priority of the frame that it wants to transmit, the token travels the ring until it reaches the station that urgently needs it. 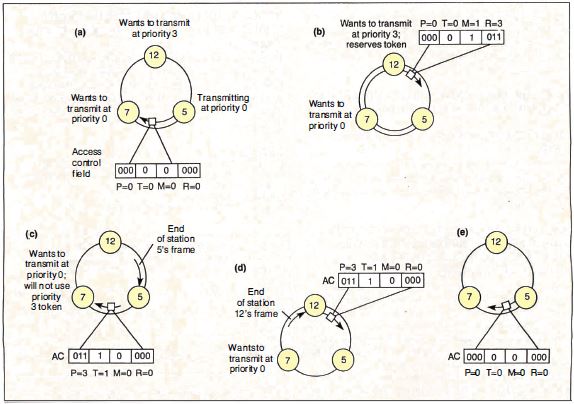 Figure 5: Placing a reservation. (a) Station 5 is transmitting a frame to station 7 on the ring. Normally, station 7 would be the next node to get the token, even though station 12 had a higher-priority frame to transmit. (b) Station 12 sees that the reservation field of the frame is less than 3 and places a 3 there. The frame continues back to station 5, which absorbs the frame and emits a token. (c) The token emitted by station 5 had priority 3, so station 7 does not use it. The token continues on to station 12, which uses the token to transmit a frame. (d) When station 12 has finished transmitting, it releases a token, still at priority level 3. (e) Station 5 receives a token at priority level 3 and "remembers " that it was the one to raise the priority of the token. It therefore restores the priority to 0 so that station 7 will have a chance to transmit. Figure 5 shows an example of the Token Ring's reservation system at work. In the simple three-node ring shown, with nodes at 5, 7, and 12 o'clock, station 5 is transmitting. Station 7 would normally use the token next, followed by station 12. But since station 12 has an urgent message to transmit, it changes the reservation field at the beginning of station 5's frame. Station 5 honors the reservation, emitting a priority token that station 7 cannot use. Once station 12 is through transmitting and the frame has completed its circle, station 12 strips its frame from the ring and passes the priority token onward. The priority token completes its loop (being used in turn by any other nodes having urgent messages) until it returns back to station 5 (which originated the priority token) . Station 5 then demotes the token to a lower priority and gives station 7 its turn. The Token Ring priority system has some especially nice properties. First, the priority of the token is always restored by the same node that raised it. Thus, a request for a high-priority token does not destroy the round-robin scheme on a lower level. Second, it can recursively nest on all eight possible priority levels. Suppose, for instance, that station 5, from the previous example, had placed a reservation for priority level 6 while station 12 was transmitting (see figure 6) . Station 12 would elevate the priority of the token exactly as station 5 did and allow it to circulate. Station 12 would then restore the priority to 3. Station 5, in turn, would restore the priority of the token to 0 again. 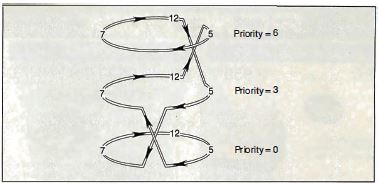 Figure 6: If, in figure 5, station 5 had placed a reservation for priority level 6 while station 12 was transmitting, station 12 would elevate the priority of the token, allow it to circulate, then restore the priority to 3. Station 5, in turn, would restore the priority of the token to 0 again. You can now see why the active monitor watches for recirculating priority tokens. Since each station that raises the priority of a token is responsible for lowering it again, a recirculating priority token indicates that a node has malfunctioned. This scenario demonstrates only two levels of nested priority, not the most complicated (seven-level) case. But no matter how deeply priorities are nested, the result is the same: Round-robin order is maintained on each level, and the next node to transmit is always the one with the highest priority. These orderly and evenhanded procedures for selecting the next node to transmit pay off especially well under heavy loads. When many nodes contend for use of the network, a 4-Mbps Token Ring can perform nearly as well as a 10-Mbps Ethernet, while a 16-Mbps Token Ring can provide more than double the throughput. I've already discussed one way in which faulty equipment can be removed from the Token Ring: the phantom circuit. Nodes that don't pass a thorough self test verifying that they can communicate properly with the rest of the ring remove themselves from the network. A more subtle feature, however, is the Token Ring's ability to localize intermittent faults and noisy links. As you may recall, each node examines every token or frame it sees and sets the error-detected indicator if it detects any errors. The error-tracking process does not stop there. Each node maintains an internal count of how many times it set the EDI. Network management software can access this counter. If there is an intermittent or noisy path in a Token Ring network, the system can always track it down to a specific stretch of cable (a "failure domain") by determining which node is just downstream. In certain cases, it's also possible to bypass a run of cable that has been completely destroyed. Look at figure 7 and notice the backup path. When two or more MAUs are connected in a ring, this path goes unused, because the ring goes in one end of each MAU and out the other. 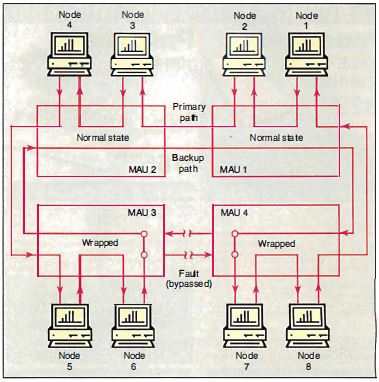 Figure 7: The Token
Ring can reconfigure itself to bypass shorts or breaks
in a cable. In this diagram, the ring continues to
function despite a cable break between MAU 3 and MAU 4.
|